Why Powered USB Is Needed? :The Short History of USB
February 1, 2011 2 Comments
This article describes a version of USB that is not related to the new USB 3 spec that Intel has released for 2010 products
The Universal Serial Bus, or USB, is right now the most common serial peripheral bus in existence. Allowing all the most common devices to connect to your computer, to each other, through hubs, and now even wireless USB has become the dominant method of low bandwidth communications between devices and their peripherals.
However, USB is not without flaws, in fact, it has tons of issues that other less accepted standards have already solved, and USB has either not solved them or solved them only recently. One of those problems is that, although USB does provide electrical power to peripherals, it is rarely enough to run devices that suck juice like no tomorrow. Powered USB exists to solve this problem.
 I will tell you why Powered USB will never be widely accepted, and also why we need it. However, to do so, this article is split into two three parts: the first part discusses the history of USB and previous peripheral ports, and why it it became widely accepted, the second part contains the meat of my argument on why Powered USB is both needed, yet failing to be accepted, and the third part describes a possible future USB 3 specification in detail.
I will tell you why Powered USB will never be widely accepted, and also why we need it. However, to do so, this article is split into two three parts: the first part discusses the history of USB and previous peripheral ports, and why it it became widely accepted, the second part contains the meat of my argument on why Powered USB is both needed, yet failing to be accepted, and the third part describes a possible future USB 3 specification in detail.
This is part 1. Part 2 is available here, and part 3 is available here.
Short History of Common Yet Totally Incompatible Peripheral Bus Implementations
Way back at the beginning of time, before Pentiums, before laptops, even before CDs, there was the IBM PC. Although not the first of its kind, it was the first home computer that took off, and along side it riding the new technology boom was the Apple II.
That said, the IBM PC had something unique for its day: a keyboard that wasn’t built into the case. The plug this keyboard used was typically called the AT keyboard port1, named after the IBM PC-AT family of computers. This plug was about a half an inch in diameter, round, and had 5 pins.
This wasn’t the only peripheral socket that IBM PCs had. Some had serial ports (using the RS-232 9-pin or 25-pin standards) going by the name of COM ports. Also featured on some IBM PCs was the Centronics parallel port (using a DB-25 style plug) going by the name of LPT or Printer ports.
So, now, we have three plugs on the IBM PC: one for your keyboard, one for low bandwidth devices (such as dial-up modems and mice when they came into the picture), and one for high bandwidth devices (such as printers, or Iomega Zip drives and external CD burners when those showed up). Does it end there? No.
A bit of time later, Creative Labs added a Joystick/MIDI dual function port on their SoundBlaster series of sound cards. IBM added a new pair of ports called PS/2 ports that used two small quarter-inch 6 pin plugs for the keyboard and mouse (replacing the AT keyboard and serial mouse combo). External SCSI showed up allowing SCSI drives in special external enclosures, and even some document scanners used SCSI as well.
Notice up to this point I have only written about the IBM PC. The Apple II I mentioned earlier had it’s own series of plugs that served the same exact functions. Apple II series computers had serial ports (not including the standard RS-232 serial ports which were compatible), ports for external floppy drives, ports for joysticks, ports for external hard drives. Macs shipped with the Apple Desktop Bus (ADB) for keyboards and mice, and the Apple IIGS shipped with ADB ports as well (in fact, before Macs did, although the Mac design team invented ADB).
None of the ports on the same machine were compatible with each other, and (except for external SCSI and RS-232 serial) none of the ports that served the same function that were used on IBM PCs and Apple computers were compatible with each other either. Confusing, isn’t it?
So, by the mid 1990s, there were a multitude of plugs all serving essentially the same tasks over and over, and all of them doing it incompatibly. USB was born for one specific purpose: to get rid of all these different ports and combine them into one big peripheral plug standard.
One Port To Rule Them All
In 1996, the USB Working Group brought forth USB, the best thing to happen to computer peripheral design in a long time, and within 5 years most if not all of the devices I mentioned before were using USB. You could get keyboards, mice, joysticks, printers, scanners, external media drives, external hard drives, dial-up modems, and a hundred other things with USB plugs.
Now you could build a computer with only two or three kinds of plugs and never have to worry about how to explain to your grandmother what the difference between SCSI and PS/2 is and why she can’t plug her new printer into either of them.
By 1998, all Apple Macintoshes2 were also shipping with USB, and they dropped the legacy ADB design as well. By 2000, some computers were shipping with hardly any legacy ports at all, and laptops went down to the bare minimum of two or four USB plugs with a parallel port (due to the corporate world still having tons of really old printers and that they wouldn’t replace until they stopped functioning) and sometimes PS/2 plugs if you were lucky.
The USB designers did foresee you wanting to use your old devices, however: there are USB converters for parallel port, serial port, PS/2 port, and SoundBlaster joystick devices so you never have to leave devices behind if you don’t want to. In addition, there are port converters for almost any other simple type of device out there, so USB really opened the doors for this sort of thing; the icing on the cake, of course, was when someone made converters to turn controllers from virtually any classic or current game system into USB gamepads.
USB solved a very important problem: we had too many competing plug designs. Not only was it confusing for end users, it was costly. Why have six plugs of all unique designs, when you can have six plugs of all the same superior design?
USB also solved another very important problem: when you have four plugs, you will have eight or more devices to plug in. The USB standard added concentrator hubs to allow the end user to plug a bunch of devices into a single plug and have all the devices work normally.
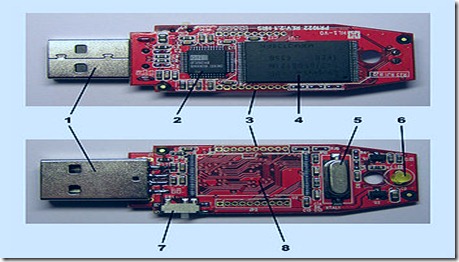
USB, while on a roll, partially fixed a third very important problem: some devices require a small amount of power, and it’s a hassle to run yet another cable to an AC adapter (for laptops in the field, this wouldn’t even be possible). USB provides some power to devices, up to a half an amp at 5 volts. You can run almost anything on this except traditionally large devices like printers, some scanners, external media drives, and hard drive enclosures3; those require external power supplies. In addition, though this wasn’t intended when the USB Working Group designed USB, some devices recharge their batteries via USB, including a brand of AA batteries that they themselves recharge over USB.
This partial fix of the third problem is where Powered USB comes in.
Read part 2.
[1]: The IBM PC-AT was the second generation of IBM PCs. The first generation, although using the same exact plug for the keyboard, did not have compatible keyboard types.
[2]: I’d like to say thanks to Steve Jobs, for if it wern’t for Macs pushing USB, they wouldn’t have become popular on PCs; before that, they were only shipping with maybe one or two plugs plus PS/2 keyboards and mice.
[3]: This is not entirely true. There are a couple USB hard drive enclosures for 3.5″ hard drives that use 2 plugs to get 1 amp, and most 2.5″ drive enclosures run on half an amp (usually) fine. It is considered a bad hack to use the two plug method required by drive enclosures, and I suggest if your enclosure offers the use of an AC adapter, use it.